
WordPress Security and Spam Prevention Tips
Updated on 2022-11-09
Contents
- 1 – Introduction
- 2 – Security Tips
- 2.01 – Firewall Plugin
- 2.02 – Usernames Can Be Changed
- 2.03 – Deny Access to Sensitive Files
- 2.04 – Hide Your WordPress Admin Login Username
- 2.05 – Restrict Access to Your WordPress Admin Login Screen
- 3 – Spam Prevention Tips
- 3.01 – AntiSpam Bee Plugin for Comment Spam Prevention
- 3.02 – FormSpammerTrap for Contact Form Spam Prevention
- 4 – List of Some of the Tip Sources
1 – Introduction
As of the date of this post, I’ve been blogging for almost 4 years and I’ve compiled and use a collection of tips for securing WordPress and preventing spam. I thought it would be helpful to display the tips in one post so that others would not have to search for them like I did. Most of the tips I came across via Internet searches when trying to resolve a security or spam issue I encountered, but I encountered one tip just by reading aother blog.
I will first cover security tips that I’ve learned and then I will cover spam prevention tips.
All of the plugins or software mentioned in this post are free to use. However if you are able to do so, you should consider donating to the creators for their efforts.
2 – Security Tips
In this section, I will be covering the following security tips:
- using a firewall plugin
- changing your username
- denying access to sensitive files
- hiding your WordPress Admin username
- restricting access to the WordPress Admin login screen
2.01 – Security Tips – Firewall Plugin
One of the first security tips I learned was to use a firewall plugin to thwart attacks on, and block known malicious users from, your site. I went through Grayson Bell’s free Understanding WordPress course before I began blogging in WordPress and in that course Grayson emphasized the importance of using a firewall plugin to secure your WordPress site. I looked at the Sucuri Security and Wordfence Security plugins and I decided to use the Wordfence Security plugin.
The Wordfence Security plugin can send weekly activity report emails showing security related activity on your site such as blocked malicious users, successful and unsuccessful login attempts, recently modified files, and whether any updates are needed.

Some of the same information is also displayed under the WordPress admin dashboard by default.

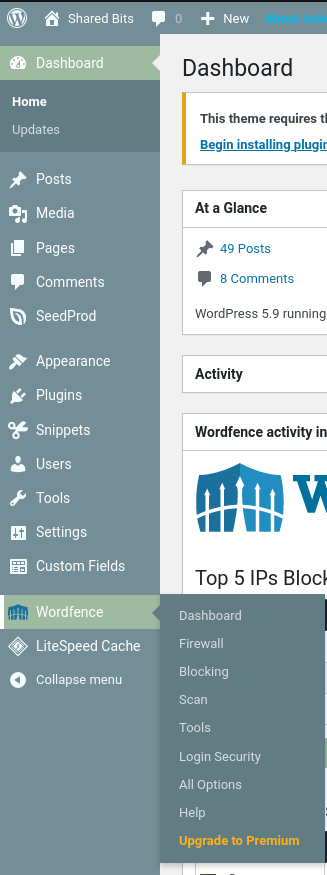
More detailed information and option settings are available under the Wordfence page accessible from the WordPress admin panel menu.
In the latter part of 2019, I discovered via a Wordfence Security weekly activity report email that someone had figured out the username for one of my logins. I have separate logins for my live site and for my sandbox/testing site. The Wordfence Security weekly activity report emails frequently show blocked known malicious users who have attempted to access my site. Having the Wordfence Security plugin for my site gives me great peace of mind.
Pesky miscreants attempting to log into your WordPress admin dashboard? Lock them out using the Immediately lock out invalid usernames setting under the Brute Force Protection section of the firewall settings.
2.02 – Security Tips – Usernames Can Be Changed
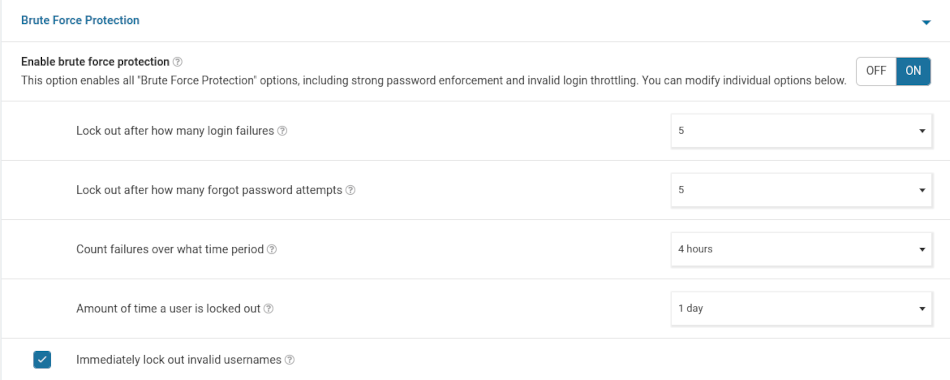
When I decided to begin blogging, I knew I wanted to have a sandbox or test site so that I could try out or test things before implementing them on my live site. After creating my live site, I created my test site by creating a copy of my live site. Creating a copy of my live site resulted in having the same username for both my live site and my test site. I thought I could change my username via my profile page under the WordPress Admin Panel, but the username field is grayed out with text next to it stating that the username cannot be changed. Not knowing any better at that time, I lived with having the same username for both my live site and my test site for about a year.
Note: Your username is normally displayed in the username field on your Profile page under the WordPress Admin Panel. For obvious security reasons, I’ve removed my username in the above screenshot.
About a year later, I discovered that someone had learned my username and was attempting to login to my WordPress Admin area. You can read more about the incident under section 2.04 – Hide Your WordPress Login Username.
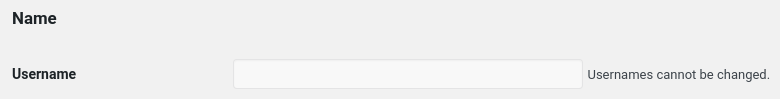
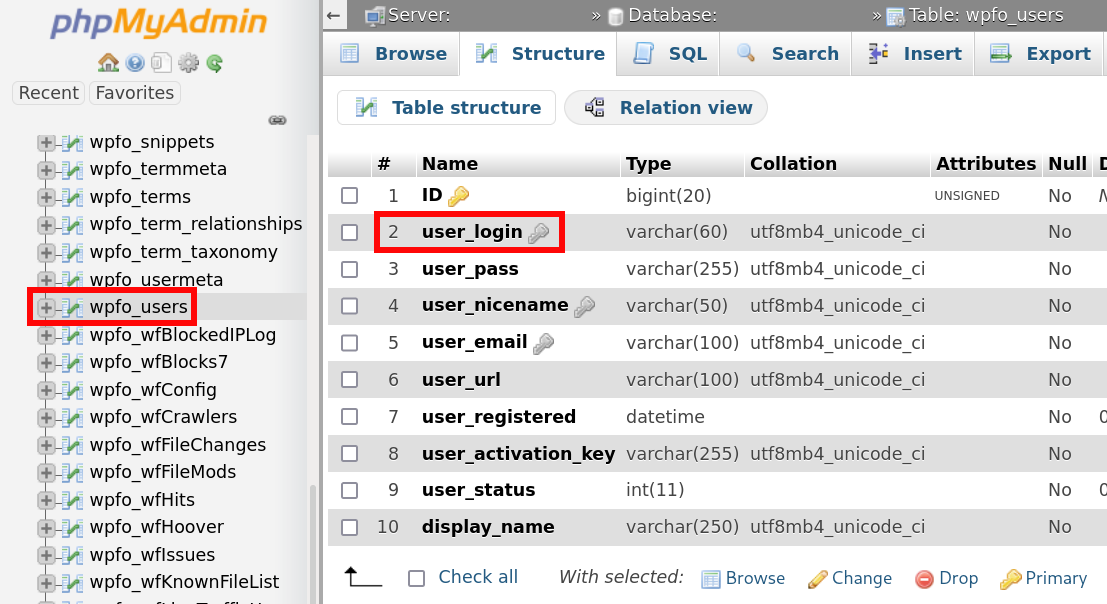
After a bit of Internet searching, I learned that the username can be changed by using phpMyAdmin under cPanel to edit the user-login field under the wp-users or similarly named table (it’s wpfo_users under my hosting account).
2.03 – Security Tips – Deny Access to Sensitive Files
WordPress contains a number of sensitive files; e.g. wp-config.php and install.php. Check the .htaccess file under your site’s root folder (e.g. public_html) to see if it has the entries listed below. If your .htaccess file is missing some or all of the entries, you should add them to deny outside access to the sensitive files.
Before making changes to your .htaccess file, make a backup copy by copying and renaming it something like .htaccess.bak or .htaccess.YYYYMMDD-##, where YYYY is the current year, MM is the current month, DD is the current day, and ## is an incremental number. The backup copy will come in handy should you make a mistake or desire to easily rollback to a previous configuration.
# BEGIN deny access to sensitive files in WordPress # disable directory browsing from the Web Options All -Indexes <files .htaccess> Order allow,deny Deny from all </files> <files readme.html> Order allow,deny Deny from all </files> <files license.txt> Order allow,deny Deny from all </files> <files install.php> Order allow,deny Deny from all </files> <files wp-config.php> Order allow,deny Deny from all </files> <files error_log> Order allow,deny Deny from all </files> <files xmlrpc.php> Order allow,deny Deny from all </files> # END deny access to sensitive files in WordPress
Note: The Wordfence Security team does not recommend disabling xmlrpc.php. You can read about their reasoning in their blog post regarding the subject. However, I’ve disabled outside access to the xmlrpc.php file for almost 3 years without any issues of which I’m aware.
2.04 – Security Tips – Hide Your WordPress Admin Login Username
In the latter part of 2019, I discovered via a Wordfence Security weekly activity report email that someone had figured out the username for one of my WordPress Admin logins. I have separate logins for my live site and for my sandbox/testing site. I was dumbfounded; how in the world could someone guess the username for one of my logins?
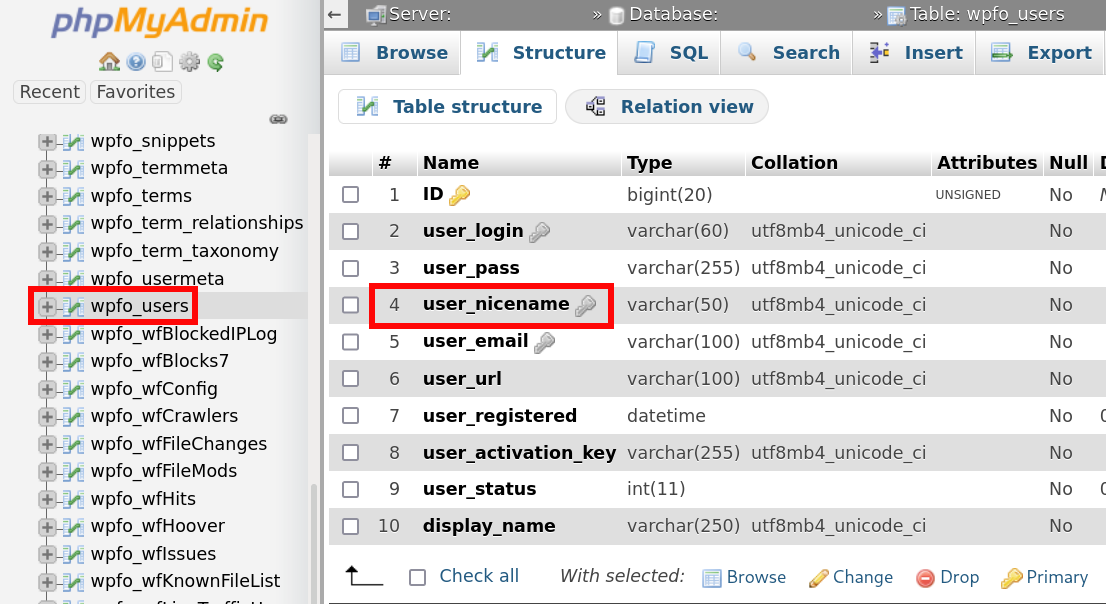
After a bit of Internet searching, I discovered that there’s a field called user-nicename under the wp-users or similarly named table (it’s wpfo_users under my hosting account) in the WordPress database.
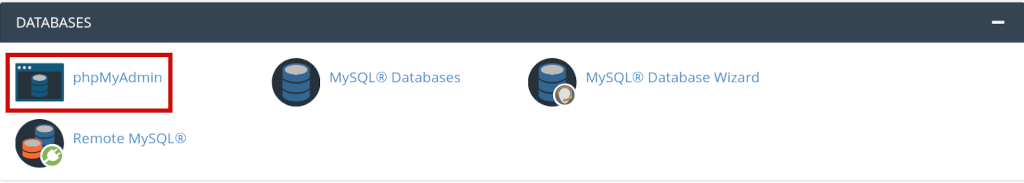
You can access the wp-users table using phpMyAdmin under the Databases section of your cPanel account.
By default, user_nicename contains your username. Supposedly there are at least a couple of methods to easily obtain the value in user_nicename.
First I changed the username for both of my sites. Then I changed the value under user_nicename to something other than my username. Details on how to change the value under user-nicename are provided in the link in the previous paragraph as well as in the list of some of the tip sources near the end of this post.
2.05 – Security Tips – Restrict Access to Your WordPress Admin Login Screen
Even though I was using a firewall plugin and I had resolved the issue of my username being discoverable, I was still bothered by seeing Wordfence Security reports of unsuccessful login attempts. I was reading through Grayson Bell’s blog in the latter part of 2019 and I discovered a gem of a tip to restrict access to the WordPress Admin login screen.
I’m not going to steal Grayson’s thunder by repeating his procedure here. His post is well written and there’s nothing I can add other than the little bit that follows below. You can use the link in the previous paragraph to read the details. However, know that for this technique to work, you need to have a cPanel account. Grayson states in his post that your hosting provider also needs to be using the Apache HTTP server. However, I am using the tip and my hosting provider uses the LiteSpeed Web server.
If your hosting provider doesn’t use Apache HTTP server, then see the last paragraph under 2.01 – Security Tips – Firewall Plugin above about using the WordFence Security plugin to immediately lockout users who attempt to login using an invalid username.
If you are using Emacs to create the special file described in Grayson’s tip, save the file with UTF-8 encoding by entering C-x f utf-8 and then C-x C-s.
After successfully implementing this tip, you will first be greeted with the following when you attempt to access your WordPress Admin login screen:
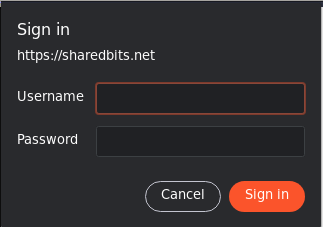
Note: The styling will differ depending on what browser you use. The screenshot above was taken from the Brave browser.
If you enter the correct credentials, you’ll be presented with your WordPress Admin login screen:
Since implementing this tip, I’ve had no failed login attempts by anyone other than myself.
3 – Spam Prevention Tips
When I first began blogging, I didn’t have any issues with spam. However, things changed when I switched hosting providers. I don’t know if the start of spam issues with the hosting change was a coincidence or not. I’m of the opinion that my last hosting provider may have had technology in place that did a better job of preventing spam.
In any case, I had issues with comment and contact form spam and for awhile, nothing I did alleviated the issue. The majority of the spam seemed to be bot related.
3.01 – Spam Prevention Tips – AntiSpam Bee Plugin for Comment Spam Prevention
To alleviate comment spam, I opted to use the Antispam Bee plugin after doing a bit of research on comment spam prevention. The Antispam Bee plugin is very easy to install and use and has quite a few setting options for tailoring your comment spam prevention desires.
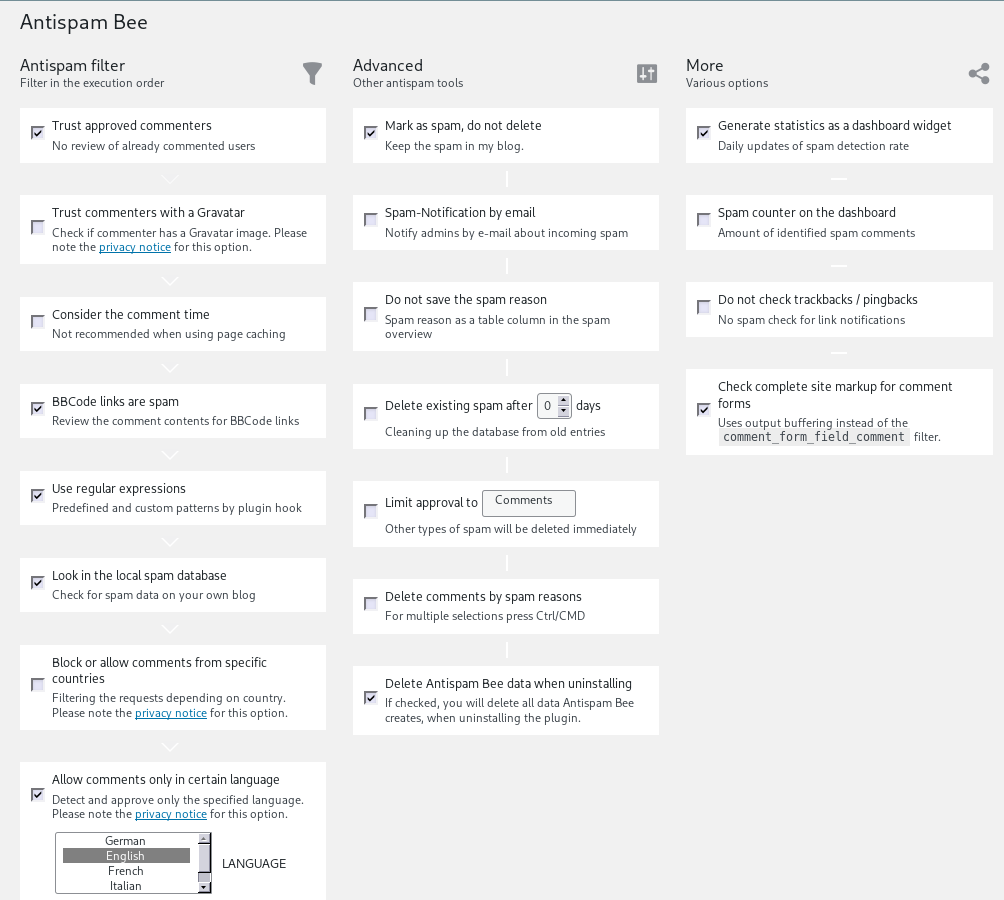
I haven’t had any issues with comment spam from bots since installing the plugin. There’s not much you can do about human spammers. Fortunately, I don’t believe I’ve had any issues with humans attempting to send me comment spam.
3.02 – Spam Prevention Tips – FormSpammerTrap for Contact Form Spam Prevention
I found and attempted to implement a DIY technique to prevent contact form spam, but that didn’t work and the technique was fairly complicated to implement. I continued my search for a contact form spam prevention solution. After spending quite a bit of time searching, I finally came across FormSpammerTrap developed by Richard Hellewell.
Implementing FormSpammerTrap under WordPress requires you to create a child theme. I was a bit apprehensive about creating a child theme because I had never created one before and I wasn’t quite sure what would happen when the parent theme was updated. However, the procedure for creating a child theme turned out to be quite simple and updates to my parent theme appear to have automatically been applied as well to the child theme.
I also modified the FormSpammerTrap code a little bit to customize it for my needs. If you know enough about HTML and CSS, you shouldn’t have any issues should you decide to modify the code for your needs.
Since implementing FormSpammerTrap, I have not received a single bot generated spam email via my contact form. Again, as with comment spam, there’s not much you can do about a real human who decides to send you spam. I was so relieved to be done with contact form spam and I was so impressed with the instructions and code, that I made a donation to Richard Hellewell for his fine product.
4 – List of Some of the Tip Sources
While most of the sources for the tips in this post already exist throughout the post, I thought it would be nice to provide a list of some of the sources in one place.
- How to Properly Change Your WordPress Username
- 10 WordPress Security Issues And How to Fix Them (link directs to tip on denying access to sensitive files)
- How to Reduce Attacks Against WordPress XMLRPC
- Hide WordPress Usernames to Improve WordPress Security
- How to Block Malicious WordPress Login Attempts with htaccess
Leave your comments or questions in the Comment box at the bottom of the page.
Post header image courtesy of gagnomn1993, at Pixabay.
2022-003




